About
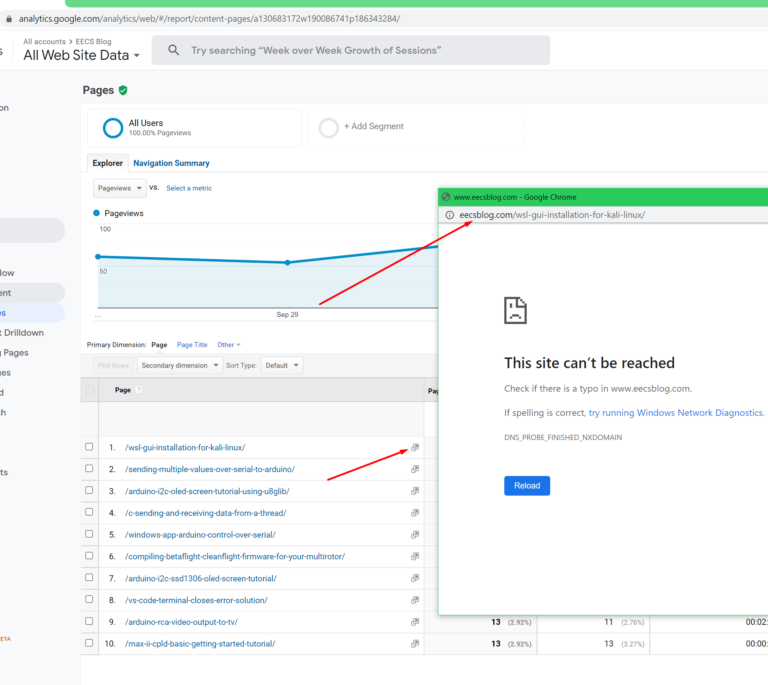
Some tome ago(few years) I was using Google Analytics to check the traffic to this very site. I was looking at the “pages report” where it shows your most visited pages. I discovered that I was getting an error(This site can’t be reached) when I click the hyperlink which was supposed to take you to that particular page on your website.
What was happening is that instead of the hyperlink pointing to the correct domain eecs.blog it was pointing to eecsblog.com. I don’t know why this happens or if it happens only to me. There might be a possibility that Google Analytics doesn’t recognize certain domains like .blog so it just adds .com at the end.
So, in theory, this opens up a possible phishing attack vector because if someone were to register eecsblog.com they could set up a phishing site and Google Analytics would be linking straight to it.
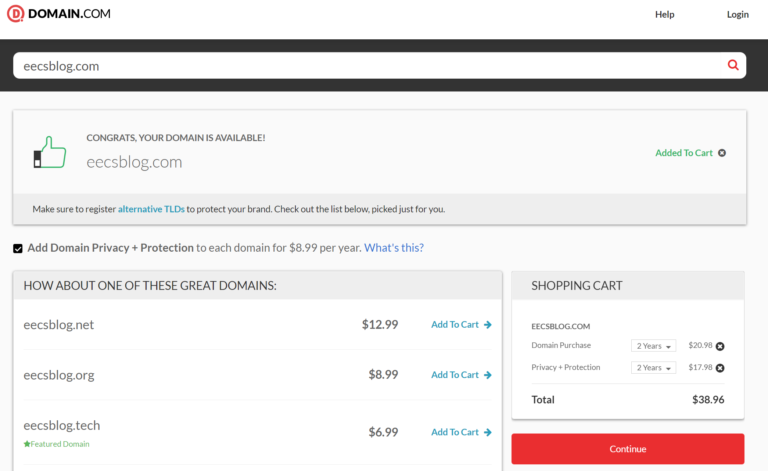
I contacted google support about this. They wanted me to buy another domain to reproduce the issue I, however, didn’t want to spend 40$ to register a domain just to potentially help narrow down a problem that is clearly on their side. I’m not spending my money to try and help a multibillion dollar company. Anyway, the case was closed down and that was that.
I decided I would still write a post about it as the issue is still present. Maybe it will help someone or someone can confirm if this also happens to them.
The chance for an attacker to successfully execute such an attack is pretty low but not impossible. It’s a type of attack that must be done to a specific target that has some value to the attacker.
You register the domain, set up the phishing site then you wait and hope that someone will be checking the analytics and click on one of the links. If they fall for it and type in their credentials you can gain access to a site and do further damage or try to login to other services as usually, people tend to reuse their passwords.